85. SafeNet KeySecure
SafeNet KeySecure devices are capable of sending their logs to a remote Syslog destination via UDP or TCP. KeySecure has four different logs: System, Audit, Activity, and Client Event. Each one has a slightly different format, and each can be configured with up to two Syslog servers. There is also an option to sign and encrypt logs messages before sending them to the remote destination. Configuration for this type of scenario is outside of the scope of this section.
2017-03-26 18:12:04 [admin] [Login] [CLI]: Logged out from 192.168.15.231 via SSHIn case of a cluster with two or more KeySecure devices, the configuration change on one of them will be replicated to other members. Each member will be sending logs separately. For more details regarding logging configuration on SafeNet KeySecure, refer to the KeySecure Appliance User Guide.
|
Note
|
This section covers configuration for sending logs via UDP. To use TCP instead, just select it instead where appropriate. |
-
Configure NXLog for receiving Syslog logs (see the examples below). Then restart NXLog.
-
Make sure the NXLog agent is accessible from the KeySecure device.
-
Configure Syslog logging on KeySecure using either the web interface or the command line. See the following sections.
|
Note
|
The steps in the following sections have been tested on KeySecure 460 and should work on other models also. |
This example shows a KeySecure Audit log message as received and processed by NXLog. Use the im_tcp module instead of im_udp to receive Syslog messages via TCP instead.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
<Extension _syslog>
Module xm_syslog
</Extension>
<Extension _json>
Module xm_json
</Extension>
<Input in_syslog_udp>
Module im_udp
Host 0.0.0.0
Port 514
Exec parse_syslog();
</Input>
<Output file>
Module om_file
File "/var/log/keysecure.log"
Exec to_json();
</Output>
{
"MessageSourceAddress": "192.168.5.20",
"EventReceivedTime": "2017-03-26 18:11:36",
"SourceModuleName": "in_syslog_udp",
"SourceModuleType": "im_udp",
"SyslogFacilityValue": 17,
"SyslogFacility": "LOCAL1",
"SyslogSeverityValue": 6,
"SyslogSeverity": "INFO",
"SeverityValue": 2,
"Severity": "INFO",
"Hostname": "p-keysecure1",
"EventTime": "2017-03-26 18:12:26",
"SourceName": "IngrianAudit",
"Message": "2017-03-26 18:12:26 [admin] [Login] [CLI]: Logged in from 192.168.15.231 via SSH"
}Additional field extraction can also be configured. Note that this depends on which particular log the message is coming from, as each has a different format.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
<Input in_syslog_udp>
Module im_udp
Host 0.0.0.0
Port 514
<Exec>
parse_syslog();
if $Message =~ /(?x)^\d{4}-\d{2}-\d{2}\ \d{2}:\d{2}:\d{2}\ \[([a-zA-Z]*)\]
\ \[([a-zA-Z]*)\]\ \[([a-zA-Z]*)\]:\ (.*)$/
{
$KSUsername = $1;
$KSEvent = $2;
$KSSubsys = $3;
$KSMessage = $4;
}
</Exec>
</Input>
{
"MessageSourceAddress": "192.168.5.20",
"EventReceivedTime": "2017-04-15 19:14:59",
"SourceModuleName": "in_syslog_udp",
"SourceModuleType": "im_udp",
"SyslogFacilityValue": 17,
"SyslogFacility": "LOCAL1",
"SyslogSeverityValue": 6,
"SyslogSeverity": "INFO",
"SeverityValue": 2,
"Severity": "INFO",
"Hostname": "p-keysecure1",
"EventTime": "2017-04-15 19:16:29",
"SourceName": "IngrianAudit",
"Message": "2017-04-15 19:16:29 [admin] [Login] [CLI]: Logged in from 192.168.15.231 via SSH",
"KSUsername": "admin",
"KSEvent": "Login",
"KSSubsys": "CLI",
"KSMessage": "Logged in from 192.168.15.231 via SSH"
}85.1. Configuring via the Web Interface
-
Log in to the KeySecure Management Console.
-
Go to .
-
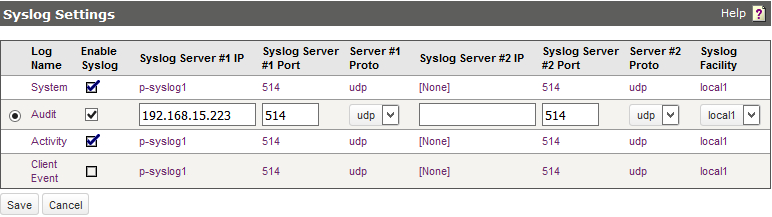
Select a log type and click Edit to change the settings.
-
Select the Enable Syslog option and specify the required IP addresses, ports, protocols, and facility for up to two servers.
-
Click Save.
-
Repeat for the other log types as required.
85.2. Configuring via the Command Line
-
Log in to KeySecure via SSH.
-
Run the following commands. Follow the prompts to enable remote syslog with the required IP addresses, ports, protocols, and facility for up to two servers.
# configure # system syslog # audit syslog # activity syslog # clientevent syslogExample 365. Forwarding System LogsThe following commands enable sending System logs to 192.168.6.43 via UDP port 514.
p-keysecure1# configure p-keysecure1 (config)# system syslog Enable Syslog [y]: Syslog Server #1 IP: 192.168.6.143 Syslog Server #1 Port [514]: Server #1 Proto: 1: udp 2: tcp Enter a number (1 - 2) [1]: Syslog Server #2 IP: Syslog Server #2 Port [514]: Server #2 Proto: 1: udp 2: tcp Enter a number (1 - 2) [1]: Syslog Facility: 1: local0 2: local1 3: local2 4: local3 5: local4 6: local5 7: local6 8: local7 Enter a number (1 - 8) [2]: System Log syslog settings successfully saved. Syslog is enabled. Warning: The syslog protocol insecurely transfers logs in cleartext